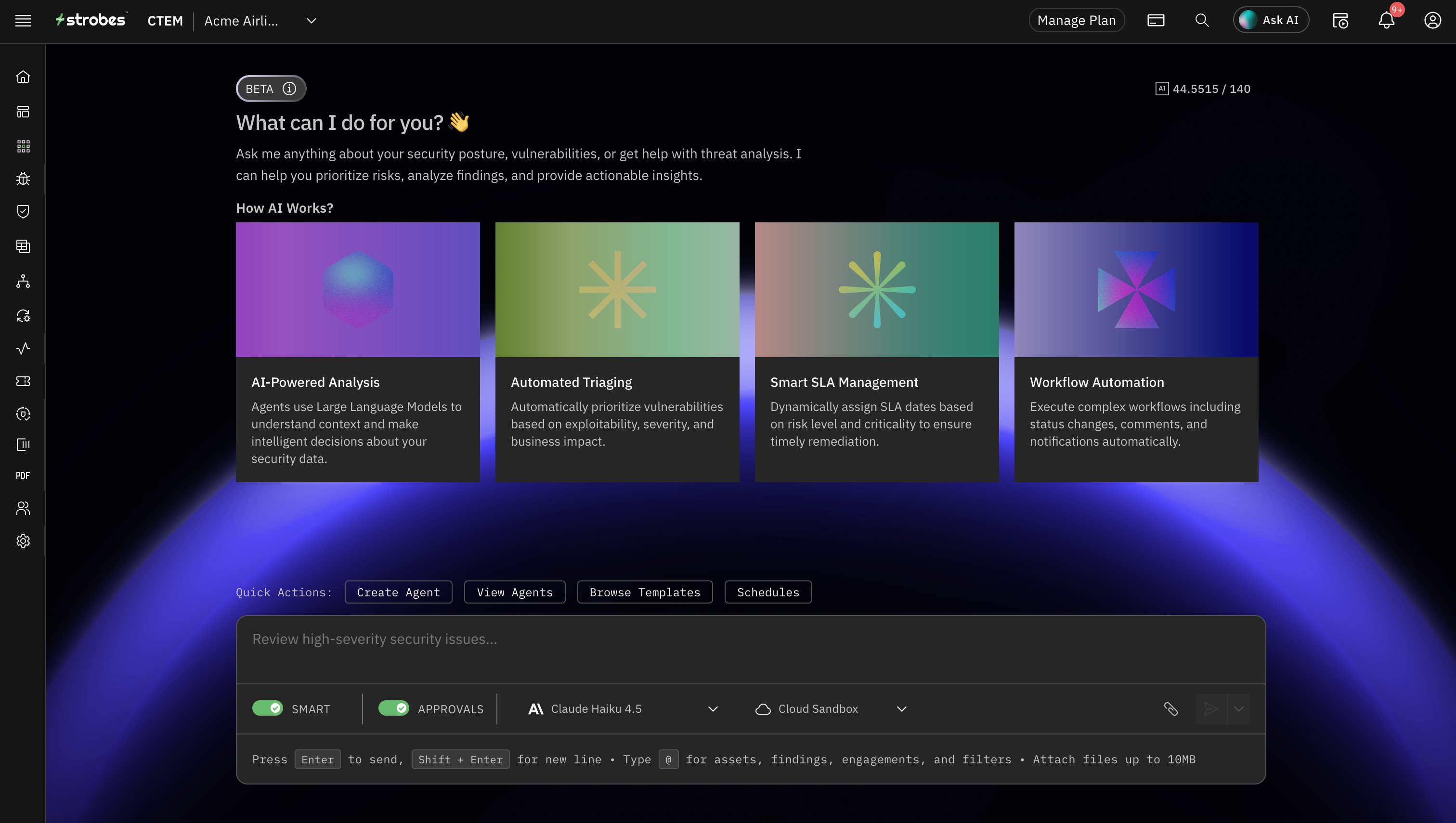
AIAgentsThatReason,Execute,andLearn
From answering questions to running autonomous security operations, Strobes AI agents work at every level of your security maturity.
Strobes AI is a multi-agent system purpose-built for security operations. Specialized agents reason across your data, execute validated workflows, and continuously improve from every engagement. You set the guardrails. You approve the actions. The agents do the work.
Watch AI agents reason, execute, and deliver
Analyzing the request to triage all critical findings and check for active exploits. First, I need to scope the query — this requires accessing the unified findings database across all connected sources. Let me check which integrations are active. I can see Nessus, Qualys, and Burp Suite are connected with recent sync data. I'll query all three simultaneously to get a complete picture of the exposure surface. Starting with the findings query — filtering for severity: critical, state: open. This will pull from the normalized data model where findings from all tools have been deduplicated and enriched with asset context. Now cross-referencing against threat intelligence sources. I need to check NVD for CVE details, EPSS for exploit prediction scores, and CISA KEV for known exploited vulnerabilities. High EPSS scores combined with KEV entries indicate immediate risk. Found CVE-2024-1234 with EPSS score 0.94 — this has a 94% probability of exploitation in the next 30 days. Checking if there's a public exploit available... confirmed, active exploit in the wild. This needs immediate escalation. CVE-2024-5678 is on the CISA KEV list — this means it's been actively exploited in real-world attacks. Cross-referencing with our asset inventory to determine blast radius and business impact. Planning agent tasks: I'll need to spawn sub-agents for browser reconnaissance to validate web-facing exposures, and a sandbox shell agent to confirm exploitability of the network-level findings. Both can run in parallel. Determining ownership for auto-ticketing — analyzing code repository mapping to identify the developers responsible for the affected services. I'll create Jira tickets with full context, reproduction steps, and remediation guidance. Setting SLA timers based on severity and asset criticality. Critical findings on production assets get 24-hour SLA with automatic escalation to the security lead if unresolved.
- Query & Deduplicate Findingspending
- Fetch from Nessus, Qualys, Burp
- Deduplicate across sources
- Enrich with asset context
- Threat Intelligence Correlationpending
- Validate Exploitabilitypending
- Remediation Actionspending
See AI agents work in your environment
Book a live demo and watch Strobes AI agents triage, validate, and remediate in real time.

AIthatanswersquestionsisn'tenough.YouneedAIthattakesaction.
Most security AI tools stop at analysis. They'll tell you what's wrong, but they won't fix it, prove it, or track whether the fix worked.
Security teams don't need more insights. They need:
- Autonomous triage that runs while they sleep, deduplicating, enriching, and prioritizing thousands of findings overnight
- Validation with evidence that proves exploitability, not a theoretical CVSS score that never translates to real risk
- Remediation workflows that execute: tickets, ownership, SLA enforcement, verification, without manual intervention
- A system that remembers: persistent context, institutional knowledge, outcomes from every past engagement
AI at every level of your security maturity
Start with AI conversation. Add supervised workflows. Graduate to full autonomy, at your pace, within your guardrails.

Your interactive security assistant. Ask natural-language questions about your vulnerabilities, assets, or risk posture. Get instant analysis with charts, data tables, and prioritized recommendations. No training required.
Teams starting their AI journey. Zero learning curve.
Interactive: ask anything about your exposure data
Multi-agent orchestration, purpose-built for security

Set Intent
Define what you want: triage these findings, test this application, report on this quarter's risk posture. Set scope, guardrails, and approval requirements. The system handles the rest.

Orchestrator Plans
The AI orchestrator breaks your request into tasks and routes them to specialized agents: triage specialists, threat intelligence analysts, pentest agents, report writers. Each agent gets exactly the context it needs.

Agents Execute
Specialist agents work in parallel. They access 100+ security tools, execute in sandboxed environments, and produce structured outputs. Complex tasks automatically spawn sub-agents. Runtime up to 2 hours.
You Approve & Verify
Approval workflows surface agent recommendations for your review. You approve, reject, or modify. Every action is logged with a complete audit trail. Re-scans verify that fixes actually worked.
Full control. Full visibility. Full compliance.

Guardrails
Three-stage protection monitors inputs, outputs, and tool execution. Custom rules for your org. Block, warn, or route to approval on any action category.

Human-in-the-Loop
Configurable approval workflows for every action category. Data modifications, external integrations, and critical decisions always require human sign-off unless you explicitly configure otherwise.

Audit Trail
Every agent action is logged: what was proposed, who approved it, when it executed, and what the result was. Compliance-ready evidence for SOC 2, ISO 27001, and regulatory audits.
Supervisor Modes
Choose your oversight level, from full manual approval on every action to monitored autonomy where agents work independently with real-time visibility into every decision.
Built to Act. Not Just Advise.
Evaluate exploitability, asset context, and threat intelligence to prioritize what actually matters. Cut triage noise by 95%.
Autonomous web, network, API, and cloud pentesting with full evidence collection and reproduction steps.
Rapid CVE impact assessment, supply chain analysis, and exploit monitoring tied to your specific asset inventory.
Create tickets, assign owners, track SLAs, and verify fixes through re-scanning. The remediation loop closes itself.
Generate board-level security briefings with risk narratives, verified metrics, and compliance evidence in minutes.
Visualize how exposures connect to critical assets and identify lateral movement opportunities before attackers do.
Scheduled security posture checks with automated alerting on changes. Exposure management that never sleeps.
7 capabilities available to agents via 100+ tool integrations
The platform gets smarter with every engagement
Not a stateless chatbot. A security partner that builds institutional expertise over time through RAG-powered retrieval and continuous learning.

Context Memory
AI Workspaces maintain full context, learnings, and institutional knowledge across sessions. Every past decision informs the next.

Skill Transfer
Techniques from one engagement transfer to the next. Triage patterns, risk heuristics, and remediation playbooks compound over time.

RAG Retrieval
Retrieval-augmented generation surfaces your org's risk priorities, historical trends, and past assessment results on demand.
Continuous Learning
Agents learn what worked and what didn't. Accuracy improves, false positives decrease, and recommendations sharpen.
“TheAIagentseliminated95%ofourtriageworkloadinthefirstmonth.Whatusedtotakeourteam3daysofmanualreviewnowhappensautonomouslyovernight,andtheaccuracyisbetterbecauseagentscorrelateacrossallourtoolssimultaneously.”
Director of Security Operations
VP Security · Fortune 500 Financial Services
AI agents power every part of the platform
Frequently Asked Questions
SeeAIagentsworkinyourenvironment
Watch Strobes AI agents triage vulnerabilities, run penetration tests, and generate executive reports, all with enterprise-grade safety and human control.
- No credit card required
- Setup in 5 minutes
- SOC 2 & ISO 27001