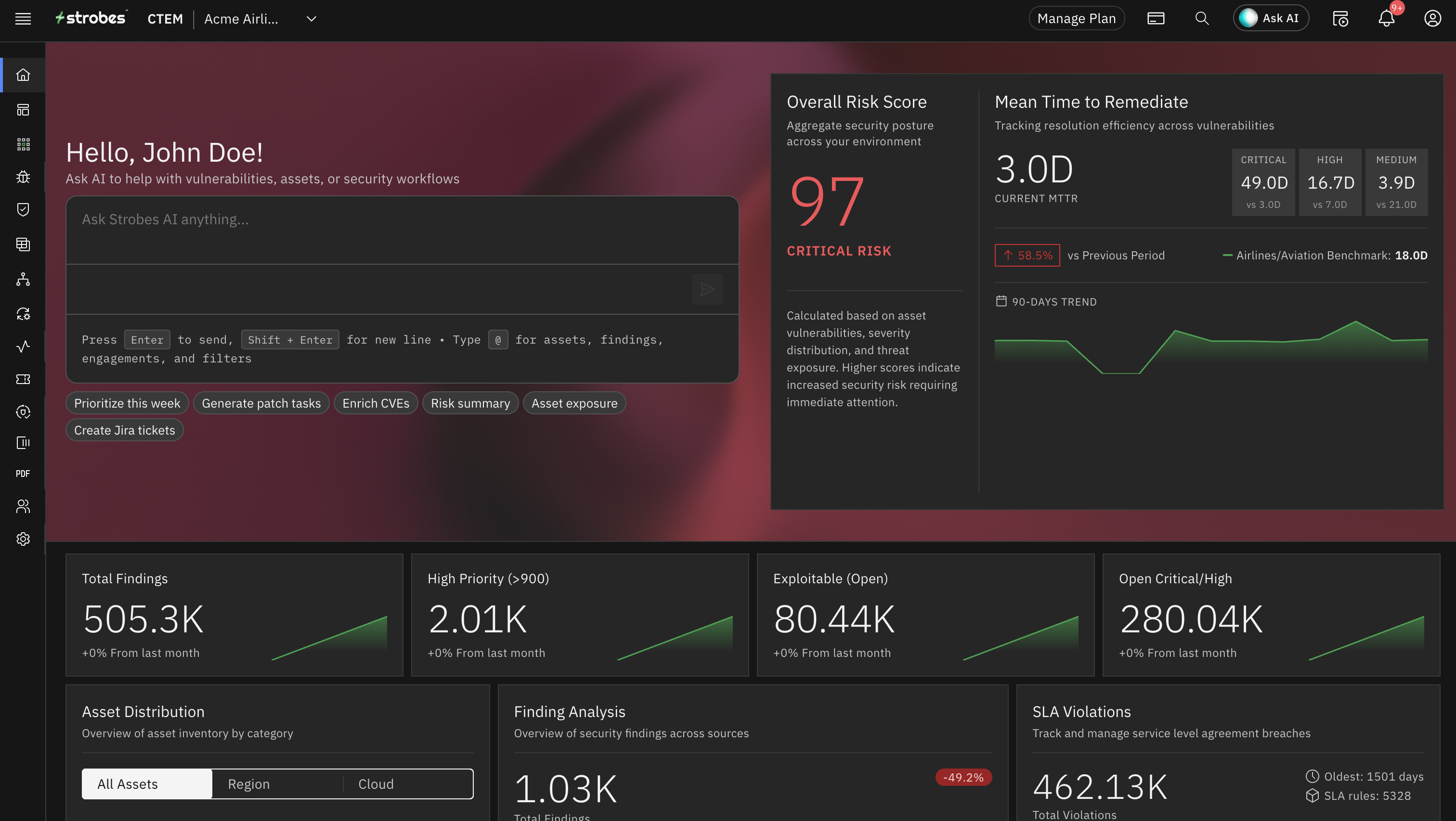
AIPentestingAgentsThatProveExploitability
Autonomous agents that execute real penetration tests — from recon to report — with working proof-of-concept for every finding. Zero false positives.
Quarterly pentests are dead. Strobes deploys specialized AI agents that crawl your applications, discover attack surfaces, chain exploits, and deliver evidence-based findings — continuously, not once a quarter. Every vulnerability comes with a working PoC, full HTTP traces, and reproduction steps.
AI agents reason, exploit, and report — autonomously
Analyzing the target scope for target.corp. This is a full web application penetration test — I need to map the complete attack surface before executing any exploits. Starting with browser-based reconnaissance. I'll use Playwright for SPA-aware crawling since modern apps load routes dynamically. Katana will handle the static crawl for sitemap, robots.txt, and JavaScript bundle analysis to discover hidden API endpoints. The authentication mechanism appears to be JWT-based. I need to test for algorithm confusion (alg:none), token forgery, and session fixation. I'll also enumerate the role matrix — admin, user, and guest — to test privilege escalation and broken access control. Now planning the injection testing phase. I'll target all user-input endpoints discovered during recon. Starting with SQL injection on search/filter endpoints — these are the most common injection points. Then moving to reflected and stored XSS, server-side template injection (SSTI), and server-side request forgery (SSRF). For access control testing, I need to systematically check every endpoint with different role tokens. IDOR testing on resource-based endpoints (/orders/{id}, /users/{id}) by swapping IDs between accounts. BOLA testing on API endpoints by manipulating object references. Critical: Every finding must be validated with a working proof-of-concept. I'll use the sandbox environment to safely confirm exploitability. PoC scripts will include full HTTP request/response captures, reproduction steps, and impact analysis. Planning ticket creation — each confirmed vulnerability gets a Jira ticket with CVSS scoring, remediation guidance, and the PoC script attached. Executive summary will aggregate risk by category.
- Recon & Attack Surface Discoverypending
- SPA crawl with Playwright
- JS bundle analysis
- Map auth flow & roles
- Injection Testingpending
- Access Control & Auth Bypasspending
- Validate & Reportpending

Quarterlypentestsfailmoderndevelopmentvelocity
Your engineering team ships code daily. Your pentest vendor shows up quarterly. By the time the report lands, the attack surface has changed completely.
Traditional pentesting suffers from three fatal flaws:
- Point-in-time snapshots — stale before the ink dries. New code, new APIs, new attack surface every sprint
- Context resets to zero — every engagement starts from scratch. No architectural memory, no accumulated knowledge
- Weeks of wait time — from scheduling to final report, the average pentest takes 4–6 weeks. Attackers don't wait
- 80% of findings are noise — theoretical vulnerabilities rated by CVSS score, not real-world exploitability
- No verification loop — you fix, close the ticket, and hope it worked. Nobody re-tests
You don't need more assessments. You need pentesting that compounds — that gets smarter with every run and proves every finding.
Proof over theory. Continuous over quarterly. Autonomous over manual.
Strobes AI pentesting agents combine the depth of a senior penetration tester with the speed and consistency of automation.

PoC or It Didn't Happen
Every finding includes a working proof-of-concept — full HTTP request/response, reproduction steps, and exploitation evidence. Zero theoretical risk. Zero false positives.

Continuous, Not Quarterly
Run pentests after every deployment, on a schedule, or on demand. Regression testing ensures fixed vulnerabilities stay fixed. Your security posture compounds instead of resetting.

Context That Persists
AI agents remember your architecture, authentication flows, and business logic. Every assessment builds on the last — techniques, findings, and attack surface knowledge carry forward.
Multi-Agent Orchestration
Specialized agents — web pentest, API security, network testing, code review, cloud audit, and threat intel — coordinated by an AI orchestrator that routes tasks optimally.
Human-in-the-Loop Safety
Configurable guardrails, approval workflows, and audit trails for every action. You set the boundaries. Agents operate within them. Full compliance with enterprise security policies.

Remediation Built In
Findings auto-sync to Jira, Azure DevOps, and GitHub with full context. SLA tracking, ownership assignment, and fix verification through re-scanning. Close the loop.
Your AI Pentesting Command Center
Monitor AI agents executing in real time — track progress across web, API, network, and access control testing. Every finding streams live with severity and PoC status.
SQL Injection — /api/users/search
IDOR — /api/orders/{id}
JWT alg:none bypass
Stored XSS — /comments
GraphQL introspection enabled
CORS misconfiguration
Broken function-level AuthZ
Rate limiting bypass — /auth/login
Eight-Phase AI Pentest — From Recon to Report
Watch AI agents execute a complete penetration test. Every phase produces evidence. Every finding comes with a working proof-of-concept. "PoC or GTFO" isn't a slogan — it's a technical requirement.
Six Specialized Pentest Agents
Each agent is purpose-built with specialized tools, knowledge bases, and exploitation techniques.
Playwright browser automation, SPA crawling, injection testing, IDOR/BOLA, business logic, race conditions, CVE exploitation
REST and GraphQL fuzzing, OAuth/JWT testing, mass assignment, BOLA detection, rate limit bypass, schema extraction
Port scanning, service enumeration, AD auditing, Kerberoasting, lateral movement, privilege escalation
SAST, dependency audit, secrets detection, crypto review, business logic analysis, reachability verification
IAM analysis, resource enumeration, S3 exposure, security group auditing, CIS Benchmark compliance
CVE enrichment, EPSS scoring, exploit availability, CISA KEV correlation, attack surface intelligence
6 capabilities available to agents via 100+ tool integrations
From intent to verified findings in four steps

Define Your Target
Provide the target — a URL, API endpoint, IP range, GitHub repo, or AWS account. Configure scope boundaries, authentication credentials, and any out-of-bounds areas. The agent handles everything else.

AI Orchestrator Plans the Attack
The orchestrator analyzes your target, selects the appropriate assessment type, and creates a multi-phase attack plan. Specialized agents are assigned to each phase based on the target's technology stack.

Agents Execute Autonomously
Multiple agents work in parallel — crawling, analyzing, injecting, validating. Each agent operates in a sandboxed environment with full tool access: Playwright, sqlmap, Nuclei, nmap, and custom exploit scripts.
Review Verified Results
Every finding is validated with a working PoC. False positives are eliminated through re-testing. Results include executive summary, technical deep-dive, CVSS scoring, and remediation guidance. Tickets auto-created in your issue tracker.
Six specialized assessments — one platform
Each assessment type deploys purpose-built AI agents with specialized tools, methodologies, and knowledge bases.

Full Web Application Pentest
8-phase methodology covering authentication bypass, injection testing (SQLi, XSS, SSTI, SSRF, command injection), IDOR/BOLA testing, business logic flaws, race conditions, and CVE exploitation.
- SPA-aware crawling with Playwright + Katana
- JavaScript bundle analysis for hidden API endpoints
- XHR/fetch interception for dynamic route discovery
- Multi-role access control testing (admin, user, guest)
- WAF detection and bypass techniques
Tools: Playwright, sqlmap, Nuclei, custom exploit scripts
How Strobes compares to XBOW and Pentera
AI pentesting is a new category. Here's how the leading platforms stack up across the capabilities that matter.
OurStandard:PoCorItDidn'tHappen
Every finding backed by a working proof-of-concept
Full HTTP traces, reproduction steps, and exploitation proof
From recon to report — every phase produces verifiable output
Teams fix what matters because every finding is real
Full control. Full visibility. Full compliance.
AI pentesting agents operate within strict guardrails — every action logged, every exploit sandboxed, every finding verified.

Scoped Boundaries
Define exactly what's in scope and out of bounds. Agents never exceed the target perimeter you set.

Complete Audit Trail
Every agent action — every request, every exploit attempt, every finding — logged with timestamps and context.

Human Approval Gates
Configure which actions require human approval before execution. Critical exploits can route through review workflows.
Credential Vault
Test credentials stored in encrypted vault with scoped permissions. Automatic rotation and revocation after assessments.
“WereplacedourquarterlypentestvendorwithStrobesAIagents.Everydeploymentnowgetstestedautomatically.Inthefirstmonth,theagentsfound3criticalvulnerabilitiesourpreviousvendormissed—withworkingexploits,nottheoreticalriskscores.”
Head of Application Security
VP Engineering · Series C SaaS Company
AI pentesting is part of a complete CTEM platform
Frequently Asked Questions
Start your first AI pentest today
Deploy autonomous AI agents against your applications, APIs, and infrastructure. Get proof-of-concept exploits for every finding — in hours, not weeks.